HID stories - Page 63
HID is a key player in the physical access control and trusted identity solutions space, focusing on innovations that enhance security, efficiency, and user experience across various sectors. Their work encompasses mobile access technologies, biometric authentication, cloud-based credential issuance, and integration of AI to advance security protocols.
Through their reports and product launches, HID highlights critical trends such as mobile IDs, AI-driven access management, sustainability in security systems, and the shift towards digital and AI-powered credentialing. By exploring HID-related stories, readers can gain insights into the evolving landscape of access control technologies, risk management in cyber and physical security, and the growing emphasis on seamless, secure user authentication methods.
Whether you’re interested in the impact of emerging technologies like AI and biometrics on identity verification or the strategic adoption of cloud solutions to streamline security operations, the content tagged with HID offers valuable knowledge for IT professionals, security managers, and technology enthusiasts looking to stay informed about advancements and challenges in trusted identity and access control.
Credential theft is the hottest trend for cyber attackers in Q2

Hands-on Review: Fortnite Battle Royale mode

What's ahead for ransomware: Seven predictions about its evolution

Securing the printing process for a revolution in ID card management

Aussie fintech shaking up invoice finance and factoring announces NZ expansion

ExpensiveWall signs users up to fraudulent SMS services

6 months under siege: the malware story so far in 2017

Windows 10 security solutions powerless against 'bashware'

Expert spells out how businesses can 'block the spears'

Cobian RAT author crowdsourcing malware botnet distribution

Avaya ANZ expands local reach with new appointments

Review: Knack 2 is a surprising improvement over the original

Interview: Hitachi on how collaboration is the key to success in the hybrid era

Are we letting the data race cloud our judgement?

Enterprise security: The hidden perils of 'unguarded talk'
Hands-on Review: Norton WiFi Privacy

It's all fun and games in the sharing economy, until the taxes aren't done
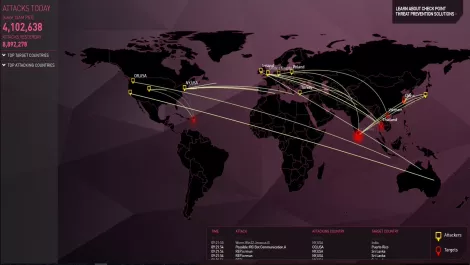
Check Point's latest threat research taken from data you can see in real time

How to drop complexity and move to a more efficient security strategy
